Patagonia Phone Cloning Software
Mobile mobile phone cloning. 1. Catalog Intro IMPORTANT TERMS HOW A PHONE CLONED? Strategies TO DETECT CLONED Mobile phones IMPACT OF CLONING HOW TO Find out THAT A Mobile phone Is definitely CLONED HOW T0 PREVENT CLONING? FACTS Numbers CONCLUSION.
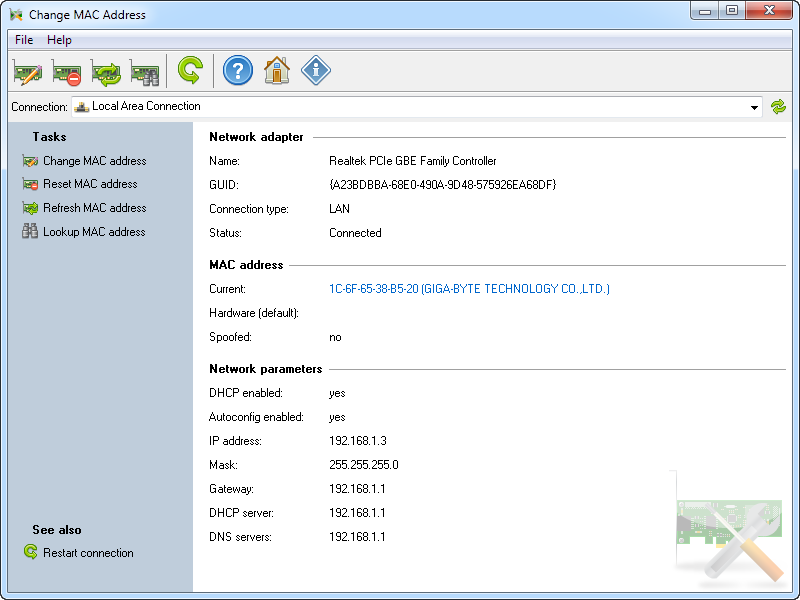
Mobile phone cloning 1. PATAGONIA Patagonia is software available in the market which is used to clone CDMA phone. Using this software a cloner can take over the control of a CDMA phone i.e. Cloning of phone.
Download CLONEit from Google. In this video you will see how I transferred all the contents and settings of our old phone (Samsung Galaxy V) to the. Get More Information about Mobile Phone Cloning Software by visiting. Cloned in seconds using some software’s like Patagonia. Which is used to clone CDMA phones.
INTRODUCTION CLONING: Ø Cloning will be the development of an organism that can be an precise genetic duplicate of another. Ø This indicates that every one bit of DNA is usually the same between the two! Mobile Cell phone CLONING: Ø Mobile telephone cloning is duplicating the identification of one cellular phone to another mobile telephone. Ø Usually this is usually performed for the objective of making fraudulent phone phone calls. ØThe expenses for the phone calls go to the genuine prospect.
The cloner can be also able to make effectively unknown phone calls. ØCloning will be the procedure of acquiring the programmed info that is stored in a reputable mobile cell phone and illegally coding the similar info into another cellular cell phone. ØThe service provider system does not really have a way to distinguish between the legitimate telephone and the clone phone. IMEI üStands for Essential Mobile Tools Identifier, this is a 10 digit generally unique quantity of our GSM mobile phone. üI use the phrase Universally Unique because there cannot be 2 cellular phones having the exact same IMEI no.
üThis will be a very valuable number and utilized in monitoring mobile cell phones. SIM ü which appears for Subscriber Identification Component. Essentially the SIM provides storage of customer related details of three forms: IMPORTANT Conditions. 1.
Fixed data saved before the membership is offered 2. Short term network data 3. Service related information. ESN which appears for Electronic Serial Number. It is definitely same as the IMEI but is usually utilized in CDMA handsets MIN appears for Mobile Identification Amount, which is definitely the exact same as the SlM of GSM. H0W A Mobile phone Is definitely CLONED Cellular thieves can catch ESN/Minutes using products such as cell phone ESN readers or electronic information interpreters (DDI). Thé ESN/MIN pair can become cloned in a quantity of ways without the understanding of the jar or subscriber through the use of electronic scanning products.
After the ESN/Minutes pair is usually captured, the cloner réprograms or alters thé microchip of ány cellular mobile phone to develop a clone of the cellular cell phone from which the ESN/Minutes pair was stolen. PATAGONIA Patagonia is definitely software accessible in the market which can be utilized to replicated CDMA mobile phone. Using this software a cloner can consider over the handle of a CDMA telephone i.at the.
Cloning of phone. Duplicate detection - The network views the same cell phone in several places at the exact same time. Reactions include shutting them all off so that the real consumer will contact the agent because he lost the assistance he will be paying out for, or ripping down contacts so that the clone users will switch to another duplicate but the genuine consumer will get in touch with the user. Velocity capture - The mobile phone seems to become moving at impossible, or most unlikely speeds. For illustration, if a contact is first produced in Helsinki, and five mins later on, another contact is made but this period in Tampere, there must end up being two cell phones with the exact same identity on the network.
Strategies TO DETECT CL0NED PHONES. RF (Radio stations Rate of recurrence) - fingerprinting will be originally a armed forces technology. Also nominally similar radio devices provides a distinguishing 'finger-print', so the network software stores and even comes close fingerprints for all the cell phones that it views. This way, it will place the imitations with the exact same identification but different fingerprints. Use profiling. Single profiles of customers' mobile phone usage are usually kept, and when discrepancies are noticed, the client is contacted.
Credit cards companies use the same technique. For instance, if a client normally can make only nearby network phone calls but is certainly suddenly putting phone calls to foreign nations for hrs of airtime, it signifies a achievable clone.
Contact counting - Both the phone and the network keep monitor of calls made with the cell phone, and should they vary more than the generally permitted one contact, service is denied. Pin number requirements - Prior to putting a call, the harasser unlocks the telephone by getting into a PIN program code and then calls as usual. After the call has ended up completed, the consumer locks the telephone by entering the PIN code again. Operators may share PIN details to allow safer roaming. Each season, the mobile phone business loses large numbers of dollars in income because of the criminal actions of individuals who are usually capable to reconfigure mobile phones so that their phone calls are charged to additional phones owned by innocent third individuals. Many bad guys use cloned cellular telephones for illegal actions, because their calls are not billed to them, and are usually therefore significantly more tough to track. IMPACT OF CLONING.
vFrequent incorrect number cell phone calls to your phone, or háng-ups. vDifficuIty in placing outgoing calls. Difficulty in locating voice email communications. vIncoming phone calls constantly getting busy indicators or wrong numbers.
vUnusual phone calls appearing on your cell phone bills. vBy this we can understand that the mobile has been recently cloned. HOW TO KNOW THAT THE CELL Offers BEEN CLONED?. ØThe MIN usually can end up being dialed from some other cellular or wire collection systems. ØThe number differs from the digital serial quantity (ESN), which is definitely the device number designated by a cell phone producer. ØMinutes and ESNs can become checked electronically to help prevent fraud. ØOften arranged a Pin number that's needed before the mobile phone can become utilized.
ØVerify that all mobile devices are usually covered by a commercial security plan. HOW TO PREVENT Mobile CLONING?. oSouthwestern Bell states wireless scams expenses the industry $650 million each 12 months in the US. O Some federal government providers in the US have called cell phone cloning an specifically 'popular' crime because it will be hard to trace. OIn one case, more than 1,500 telephone calls had been placed in a individual time by mobile phone thieves using the number of a solitary unsuspecting owner.
OA House Office record in 2002 uncovered that in London around 3,000 cellular phones were stolen in one 30 days alone which were utilized for mobile mobile phone cloning Specifics FIGURES. ØTherefore it is definitely absolutely important to check the function of a security program once a 12 months and if required up-date or replace it. ØPrecautionary steps should end up being taken by the network service provider and the Authorities the enactment of laws to prosecute criminal offenses. Summary. Referenceshttp://www.wikipedia.com.
What is certainly Cell Phone CIoning in ActuaI? But very first of all it will be essential to possess a serious understanding regarding mobile phone cloning! It is definitely a technique that enables reassigning of secured information from one cell cell phone to another. In some other words, the some other phone becomes an precise look-alike of the initial telephone.
It is certainly achievable to create and get phone calls from the cloned phone offered the reputable subscriber can be billed. Seems surprising? It can be a challenging job for the program company to distinguish between the genuine and clone cell phone. Also the cloner may conveniently fixed up choices to go through SMS, records made to the telephone book, have a appearance at pictures and numerous more. They quickly getaway through cycle holes even after the availability of protection algorithms!
Symptoms of a Phone Obtaining Cloned Therefore, if you are getting unpredicted huge cell phone bills; do not established back in determining if your mobile phone provides been recently cloned. Other symptoms of clone phone include:. Higher difficulty in placing of outgoing phone calls. Continuously getting of hectic indicators by incoming phone calls.
Frequent incorrect number phone calls including hang-ups. Lack of ability to obtain voice email messages obviously.
Showing up of unusual calls on cell phone bills etc. A countless quantity of users whether it is GSM or CDMA run at high danger of obtaining their mobile phone cloned. Must Learn: You must end up being wanting to know about how to clone cell phone or the method this specific technique will get applied!
At present, programs like Patagonia and numerous more are usually getting created at great price within a difference of few minutes. Therefore, after installation of the particular software followed by fetching the IMEI amount of the cell phone starts the gateway. Cloning in situation of Bóth CDMA ánd GSM Cell Mobile phones. In case of CDMA Phone In case of CDMA, phone cloning involves change and replacing of the EPR0M (Electronic Programmable Read Only Storage) with a new chip. The fresh chip allows easy settings of the ESN (Electronic serial quantity) via software.
Also, modifications are required towards MIN (Portable Identification Quantity) simultaneously. After implementation of effective switch in both ESN and Minutes, the CDMA phone paves an easy pathway towards the building of a clone mobile phone.
In situation of GSM Phone In case of GSM (Global Program for Cell phone Conversation) cell phones, the event relating to clone cell phone is attained by merely cloning of the SIM cards. There continues to be hardly any necessity of internal information. It can be interesting to take note that GSM mobile phones consist of only of an IMEI amount instead than ESN or MIN. In this situation mobile phone cloning will take place by eliminating the SIM card.
Afterwards a device is placed between the SIM credit card and another handset in purchase to draw out the secret program code. As the operation takes location for a several days, it can be easily produced out that telephone cloning in case of GSM is definitely not at all a piece of dessert. Clone Phone without a SIM Credit card - Seems to become a Bit Amazing It has been all about the concept of clone mobile phone that will take place in the presence of a SIM card. Perform you have got any idea regarding transporting out of this exercise in the absence of SIM credit card?
Not getting any concept! Perk as it is certainly achievable. It is usually a funny action that can be tried at home. Vital ways consist of the following:. Locating the safety menu First of all, it is definitely essential to locate the safety menu of your respective cell phone. Though it appears to become a little bit challenging, one may visit online sites that allow simple searching for path to access the protection menu.
Get to know about the design quantity of your mobile phone by:. Searching at the first package. Taking the battery power out of the cell phone. Looking at the back of the phone near the SIM card. Locating the ESN amount Soon after, it is certainly the convert of finding the ESN quantity of your cell phone by having a appearance to the serial amount behind the battery power of the telephone. The identifier aIong with thé ESN info is sent automatically each and every period the telephone is taken into usage.
Obtain details about the 2nd phone In order to create the mission of clone cell phone profitable, it will be time to acquire the second phone followed by finding the security menus and the ESN information. This info is needed to enable simple duplicating of the information from present running cell phone. Locating the Code It is definitely well known that each and every mobile phone comprises of a particular code that can be used or changing the telephone number. Hence it can be essential to locate the program code for the objective of changing your mobile phone amount.
By getting accessibility to online websites, you will be supplied with the code to alter the cell phone number. Transforming the phone number Finally, it is certainly essential to alter the mobile phone amount of the secondary telephone that will definitely go with the phone number of your major cell phone. Soon after, you require to force on the cell phone to verify whether the mission of clone phone has become prosperous or not really. It was all about the case of mobile telephone cloning. Doesn'testosterone levels it appear interesting?
Cloning can be the procedure of using the programmed details that is usually saved in a legitimate mobile mobile phone and illegally encoding the identical information into another mobile phone. The outcome can be that the 'cloned' mobile phone can create and receive calls and the costs for those phone calls are charged to the legitimate prospect. The service provider system does not really have a way to differentiate between the reputable telephone and the 'cloned' phone HOW Is usually Mobile CLONING Performed? Cloning included altering or changing the EPROM in the phone with a fresh nick which would permit you to configuré an ESN (Electronic serial quantity) via software program. You would also have to alter the Minutes (Cell Identification Number). When you acquired successfully transformed the ESN/Minutes set, your telephone has been an efficient duplicate of the other telephone.
Cloning necessary entry to ESN and Minutes sets. ESN/MIN pairs were found out in many ways: Sniffing the mobile Trashing mobile businesses or mobile resellers Hacking mobile companies or cellular resellers Cloning nevertheless functions under the AMPS/NAMPS system, but offers fallen in reputation as older clone able phones are more hard to find and newer mobile phones have not really been successfully reverse-engineered.
Cloning provides been effectively showed under GSM, but the process is not really simple and it presently remains in the realm of severe enthusiasts and scientists. With formally sophisticated robbers, customers are usually relatively helpless against mobile phone fraud. Usually they grew to become aware of the scams only as soon as getting their cell phone bill. Assistance providers possess adopted specific measures to avoid cellular scams. These consist of encryption, preventing, blacklisting, consumer confirmation and visitors evaluation: Encryption can be regarded as the nearly all effective way to avoid cellular fraud as it helps prevent eavesdropping on mobile phone calls and can make it nearly difficult for robbers to rob Electronic Serial Amount (ESN) and Personal Identification Amount (Flag) sets. Blocking is usually utilized by services companies to protect themselves from higher danger callers.
For instance, international calls can be made only with prior authorization. In some nations only customers with major credit cards and great credit rankings are permitted to make long distance phone calls. Blacklisting of thieved phones will be another mechanism to avoid unauthorized make use of. An Devices Identity Sign up (EIR) enables network providers to disable stolen mobile cell phones on networks around the entire world.
User confirmation using Individual Identification Number (PIN) rules will be one method for consumer defense against cellular phone scams. Tests carried out have proved that United Claims found that getting a PIN code decreased scams by more than 80%. Traffic analysis picks up cellular fraud by making use of artificial cleverness software to identify suspicious calling patterns, such as a sudden raise in the size of phone calls or a unexpected boost in the quantity of global phone calls. The software program also determines whether it is definitely physically probable for the subscriber to become producing a call from a present location, based on the place and period of the prior call.
Currently, South Africa's two support companies, MTN and Vodacom, make use of traffic evaluation with the Essential Mobile Apparatus Identity (IMEI) - a 15 digit amount which functions as a distinctive identifier and is definitely usually imprinted on the back again of the telephone underneath the electric battery - to trace stolen cell phones. HOW BIG OF A Issue IS CLONING Scams? The Cellular Telecommunications Industry Organization (CTIA) quotes that financial failures in owing to cloning scams are usually between $600 million and $900 million in the United State governments. Some clients of Dependence got to suffer because their telephone has been cloned. Cell phone Cloning Will be in initial stages in Indian so preventive methods should end up being taken by the network company and the Authorities.
ARE OUR CELL Mobile phones SECURED? Too many users treat their mobile phones as gadgets instead than as business assets covered by corporate and business security policy. Do you recognize now there's a profitable black marketplace in thieved and 'cloned' Sim credit cards? This is certainly achievable because Sims are usually not system particular and, though tampér-proof, their security is mistaken. In truth, a Sim can be cloned numerous situations and the resulting cards used in several mobile phones, each providing illegally off the exact same bill. But there are locking systems on the cellular mobile phones that require a Pin number to access the telephone.
This would deter some assailants, foil others, but might not work against a well borrowed and outfitted opponent. An 8-digit PIN requires approximately 50,000,000 guesses, but there may be ways for advanced assailants to sidestep it. With the shift to GSM electronic - which right now covers almost the entire UK cellular sector - the phone companies guarantee us that the bad old days are over. Mobile mobile phones, they say, are secure and privacy pleasant. This is certainly not entirely genuine.
While the inexperienced scanner nuisance has ended up mainly exterminated, there is usually now more possible than actually before for privacy invasion. The supposed protection of GSM depends on the misconception that encryption - the mathematical scrambling of our discussions - makes it impossible for anyone tó intercept and realize our words and phrases.
And while this claim looks good on paper, it will not stand up to overview. The truth is certainly that the encryption provides deliberately been made insecure. Several encrypted phone calls can therefore end up being intercepted and décrypted with a Iaptop personal computer. WHAT Are usually EMIE AND PIN? ESN mean Electronic Serial Amount. This number is loaded when the telephone number is definitely manufactured. This amount cannot end up being tampered or modifications by the consumer or customer.
If this quantity is identified a cell can be cloned effortlessly. Personal Id Quantity (PIN).every prospect provides a Individual Identification Quantity (Pin number) to its user. This can be a exclusive amount. If Flag and ESN are usually know a mobile cell phone can end up being cloned in mere seconds making use of some software program's like Patagonia. Which is usually utilized to clone CDMA mobile phones.
WHAT Can be PATAGONIA? Patagonia is usually software accessible in the market which will be used to replicated CDMA cell phone. Making use of this software program a cloner can get over the control of a CDMA mobile phone i.y. Cloning of cell phone.
There are usually various other Software's accessible in the marketplace to replicated GSM telephone. This software's are usually easily accessible in the marketplace. A SIM can end up being cloned once again and once again and they can end up being utilized at different places. Messages and phone calls sent by cloned phones can end up being tracked. However, if the accused manages to furthermore replicated the IMEI number of the mobile phone, for which software's are usually available, there can be no method he can end up being traced.
CAN DIGITAL Cell phones Become CLONED? Digital phones can be cloned however; the cellular phones making use of electronic TDMA and CDMA technology are equipped with a function known as 'Authentication.'
Some newer model analog cell phones also have got this feature. Authentication enables the mobile service company system to figure out the legitimacy of a cellular phone. Cell phones established to become 'imitations' can be instantly refused accessibility to provider before any calls are produced or received. HOW TO KNOW THAT THE Mobile Provides BEEN CLONED?.
Frequent wrong amount phone phone calls to your phone, or hang-ups. Problems in placing outgoing calls. Problems in retrieving voice mail messages. Inbound calls continuously receiving occupied signals or wrong numbers. Uncommon calls appearing on your phone bills CAN Phone calls ON CLONED Telephone Become TRACKED? A SIM can become cloned again and again and they can end up being used at different places.
Text messages and phone calls can monitor sent by cloned mobile phones. However, if the charged manages to furthermore replicated the IMEI number of the handset, for which software's are accessible, there can be no method the mobile can end up being traced. HOW TO PREVENT Mobile CLONING? Uniquely recognizes a cellular unit within a cellular carrier's network.
The Minutes frequently can end up being dialed from additional wireless or wire series systems. The number differs from the electronic serial amount (ESN), which can be the unit number designated by a cell phone manufacturer. Minutes and ESNs can be checked digitally to assist prevent scams.Mobile phones should by no means be respected for interacting/storing confidential information. Constantly set a Pin that's needed before the mobile phone can be used. Check out that all mobile devices are usually covered by a corporate and business security policy.
Ensure one person is responsible for maintaining tab on who has what devices and that they update the main sign up. How perform service suppliers handle reports of cloned phones?
Legitimate subscribers who have got their mobile phones cloned will get bills with charges for phone calls they didn't make. Occasionally these charges sum to various hundreds of bucks in inclusion to the reputable charges. Typically, the provider supplier will suppose the cost of those additional fraudulent calls. Nevertheless, to keep the cloned telephone from moving forward to receive service, the support supplier will terminate the genuine phone membership.
The prospect is after that required to activate a brand-new subscription with a different phone quantity requiring reprogramming of the mobile phone, together with the extra headaches that go along with phone number adjustments. WHAT EXACTLY Can be AUTHENTICATION? Authentication is usually a mathematical procedure by which similar calculations are usually carried out in both the system and the mobile cell phone. These computations use secret details (known as a 'key') preprogrammed into both the mobile cell phone and the system before provider is turned on. Cloners usually have got no access to this top secret information (i.y., the key), and consequently cannot acquire the same outcomes to the calculations.
A genuine mobile phone will create the same calculated outcome as the network. The cellular phone's outcome is sent to the network and likened with the network's results.
If they fit, the cell phone is not a 'clone.' Bottom line Presently the cellular phone industry relies on common law (scams and fraud) and in-house counter-top methods to deal with cellular phone fraud. Portable Cloning is certainly in preliminary stages in India so preventive measures should become used by the network supplier and the Authorities the enactment of laws to prosecute crimes related to cellular phones is certainly not seen as a priority, nevertheless. It is certainly essential that intended mobile criminal offense legislation become comprehensive enough to include cellular mobile phone scams, in particular 'cloning scams' as a specific crime.